WebNet1
Category: Forensics
Points: 450 pts
We found this packet capture and key. Recover the flag. You can also find the file in /problems/webnet1_0_d63b267c607b8fedbae100068e010422.
Similar to WebNet0, we apply the key to the packet capture in Wireshark. However, this time the flag is not in the HTTP header. If we follow the HTTP stream (right-click on an HTTP packet -> Follow -> HTTP Stream), we see this:
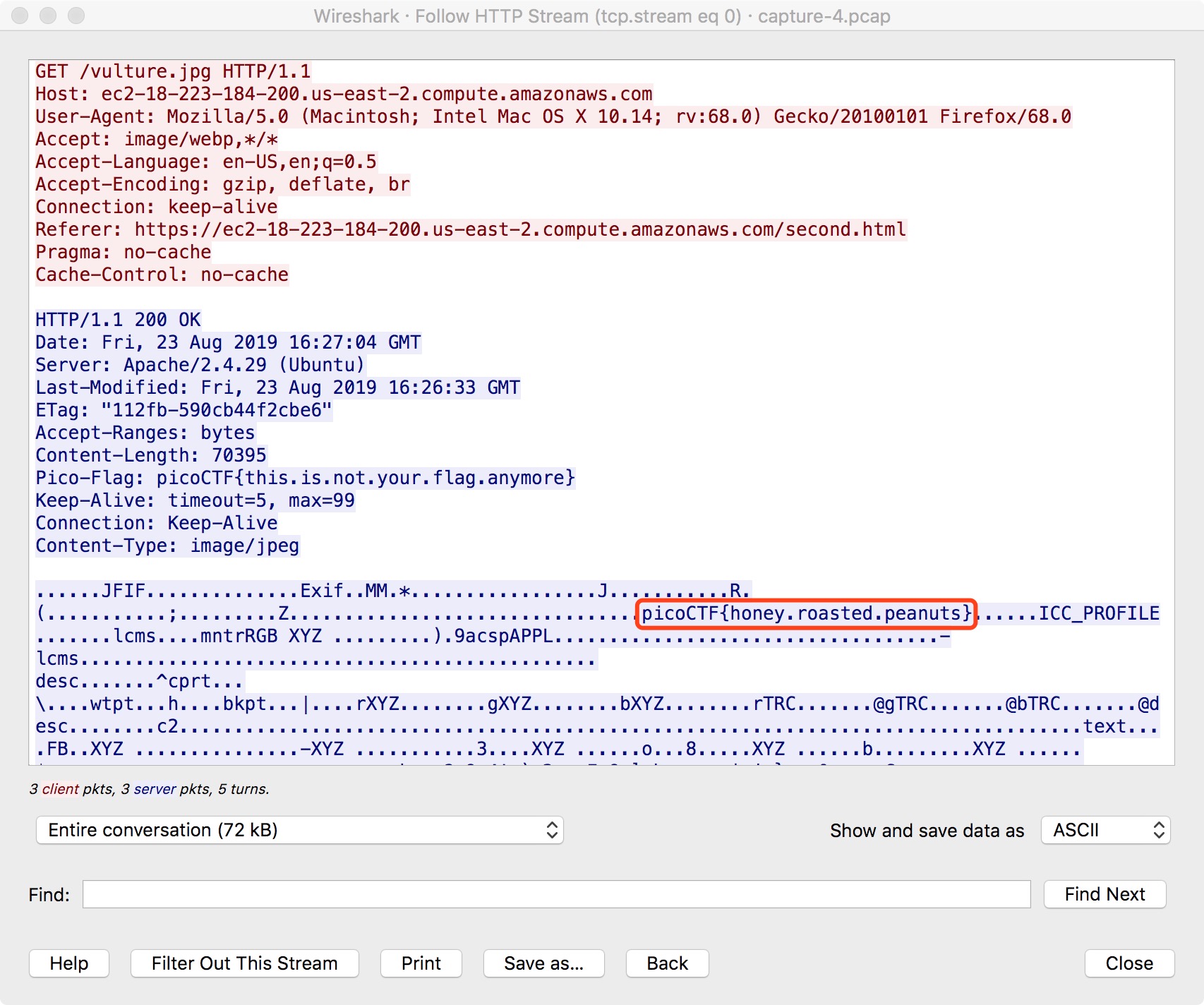
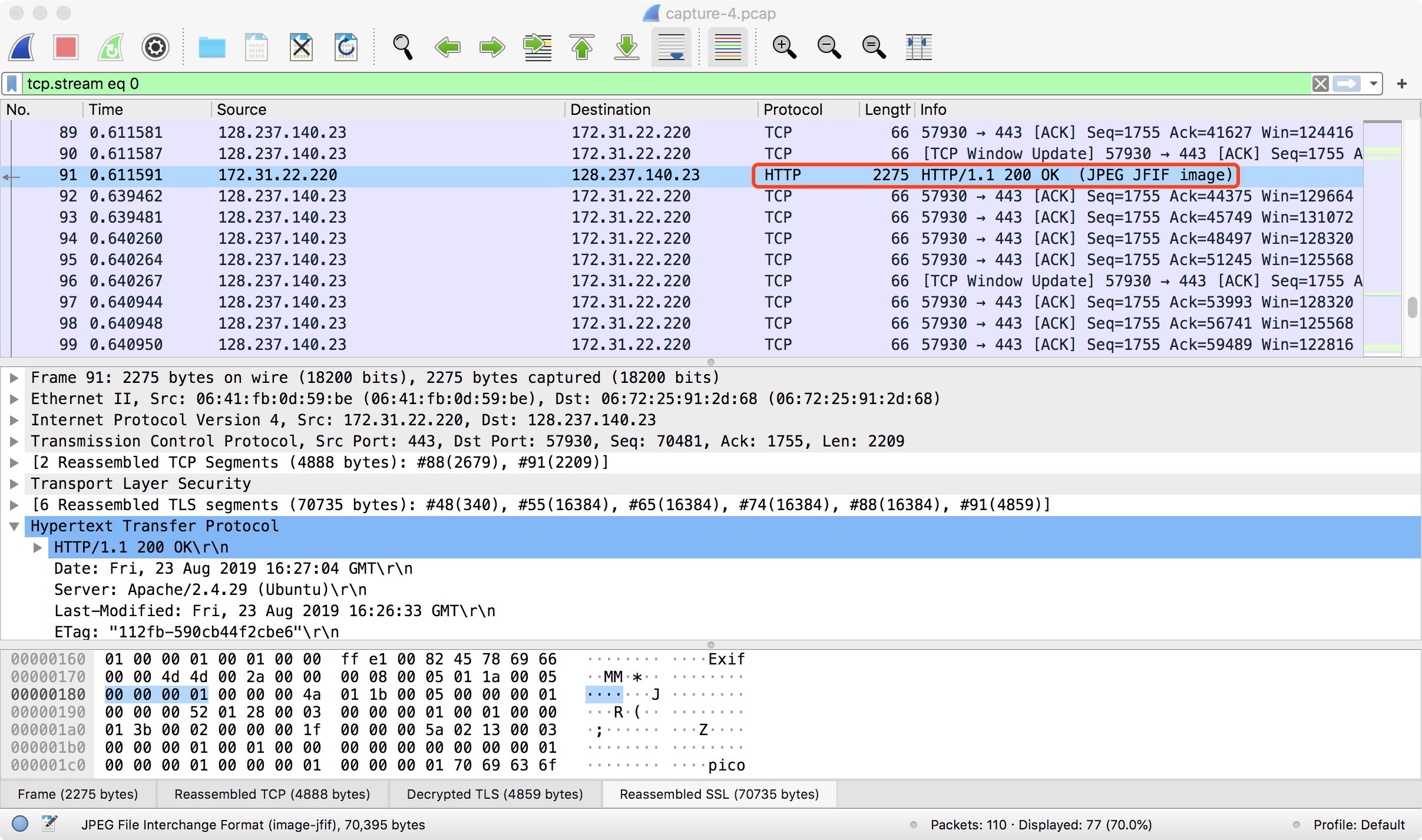
Apparently, the server is sending a JPEG-format image to the client (“GET /vulture.jpg HTTP/1.1”). We can already see the flag in the screenshot above, but just out of curiousity, we can regenerate the image from the packets. To do so, we need to click on the packet marked as “HTTP/1.1 200 OK (JPEG JFIF image)”:
Scroll down in the middle panel until we see “JPEG File Interchange Format”:
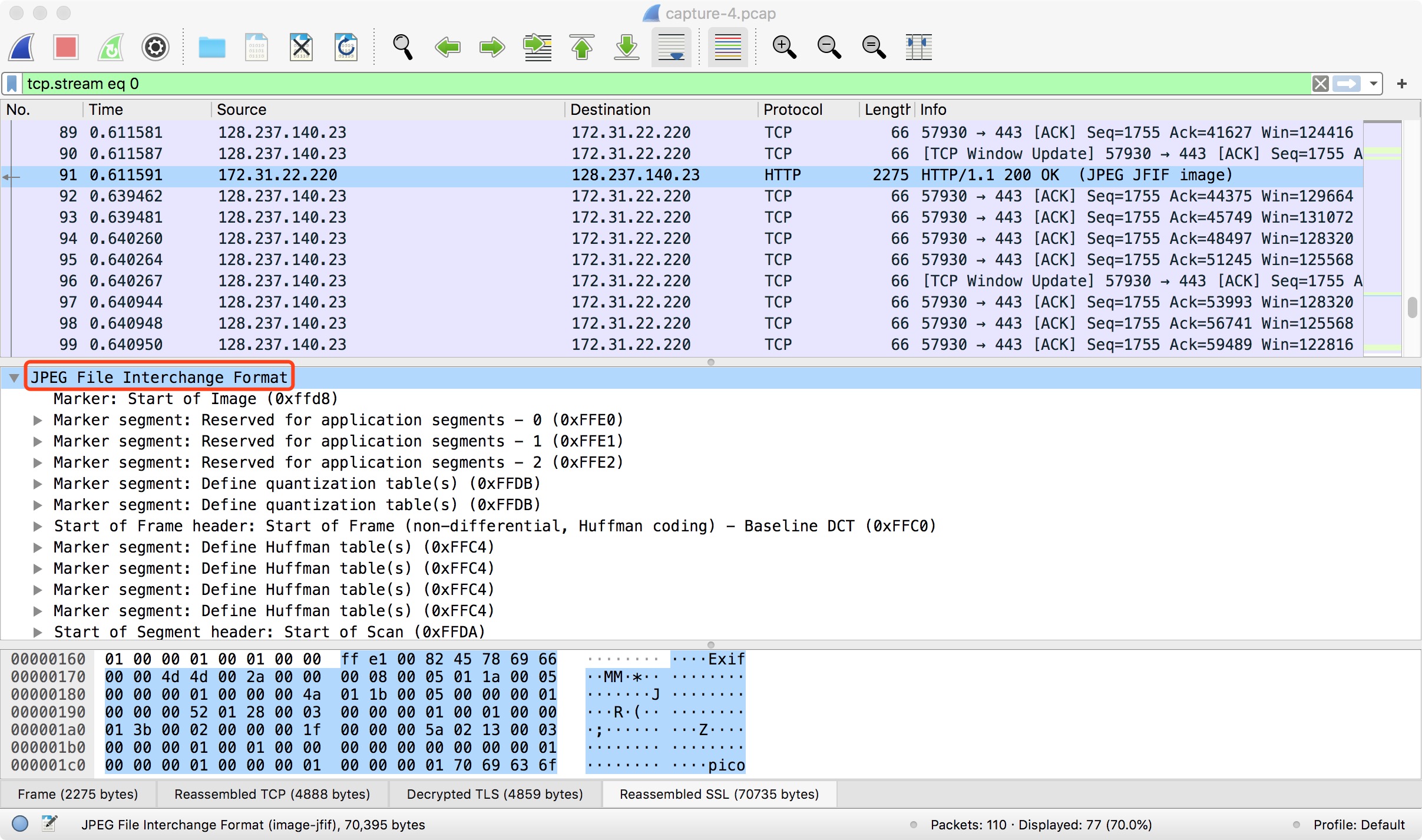
Right-click on “JPEG File Interchange Format” and select “Export Packet Bytes”. The resulting image is…
…Oh well. They did call the picture “vulture.jpg”. What did you expect?
References:
Techwalla: How to Get Images From Wireshark (Link)