Anomaly 21: Shimo La Kumwagilia
Points: Unknown
Your IDS system generated an alert for a known malicious IP, 40.122.151.219, that appears to be part of a watering hole attack. Examine the accompanying packet capture file (Anomaly 21.pcap) from the affected subnet to determine the cause of the suspicious activity. If this is a true positive, examine the associated traffic to determine whether the compromise was successful. To solve, look for the flag{\<string>} value. To answer, submit only the \<string> portion of the flag. For example, if I were to uncover the flag with value: flag{d41d8cd98f00b204e9800998ecf8427e} I would submit d41d8cd98f00b204e9800998ecf8427e for the answer.
To solve this problem, we must first know what a watering hole attack is. The attacker tracks the websites that the victim frequents, scans those websites for vulnerabilities and injects malicious code into those websites to redirect the victim to the attacker’s server. The name comes from predators in the natural world, who lurk around watering holes, waiting to prey on animals that come to drink. [1]
The provided file is a packet capture. Since we know that 40.122.151.219 is the malicious IP, we can apply the filter “ip.addr == 40.122.151.219” to look at the packets coming from and going to the malicious server.
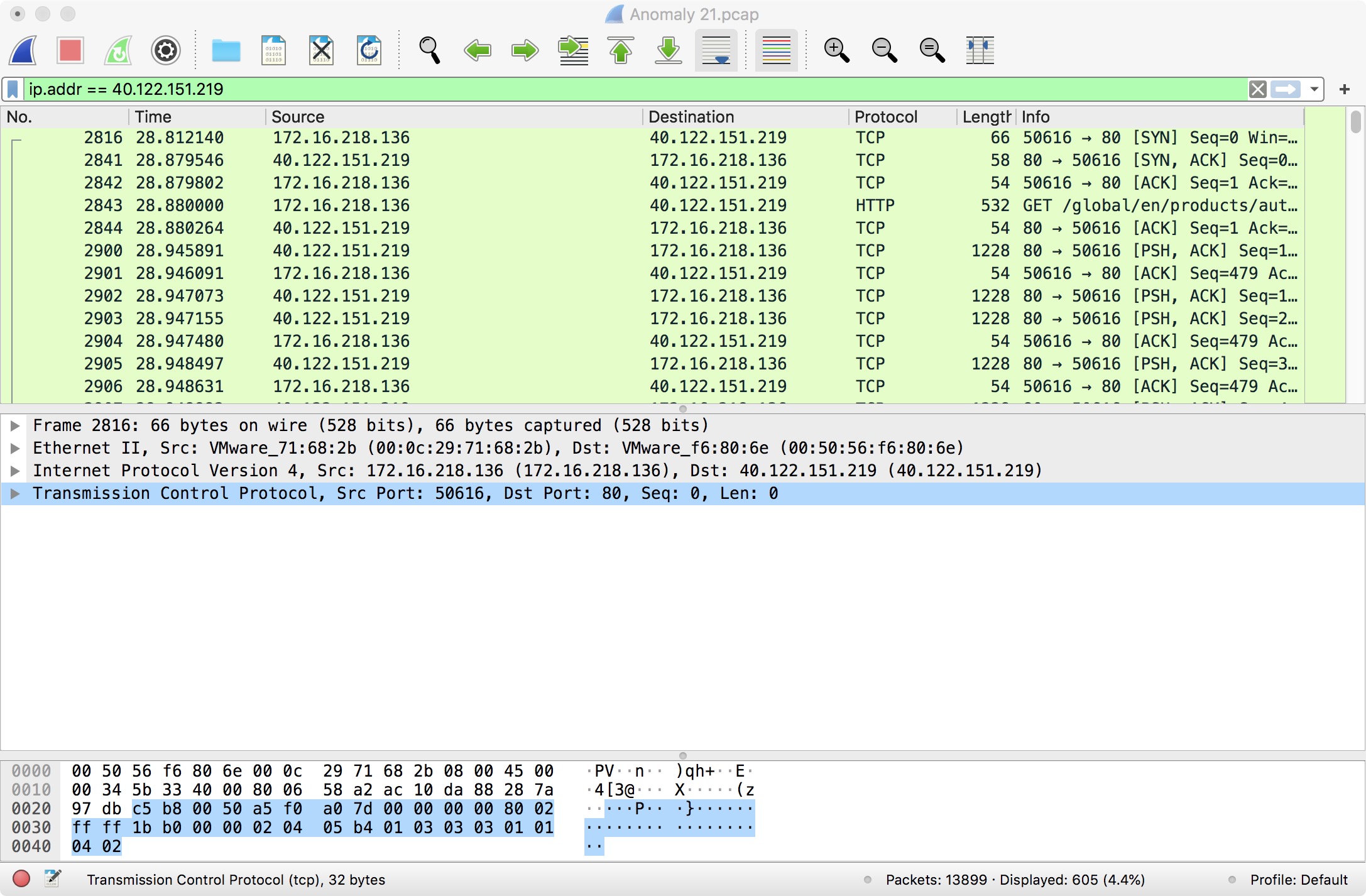
We can follow the TCP stream to see the conversation more easily:
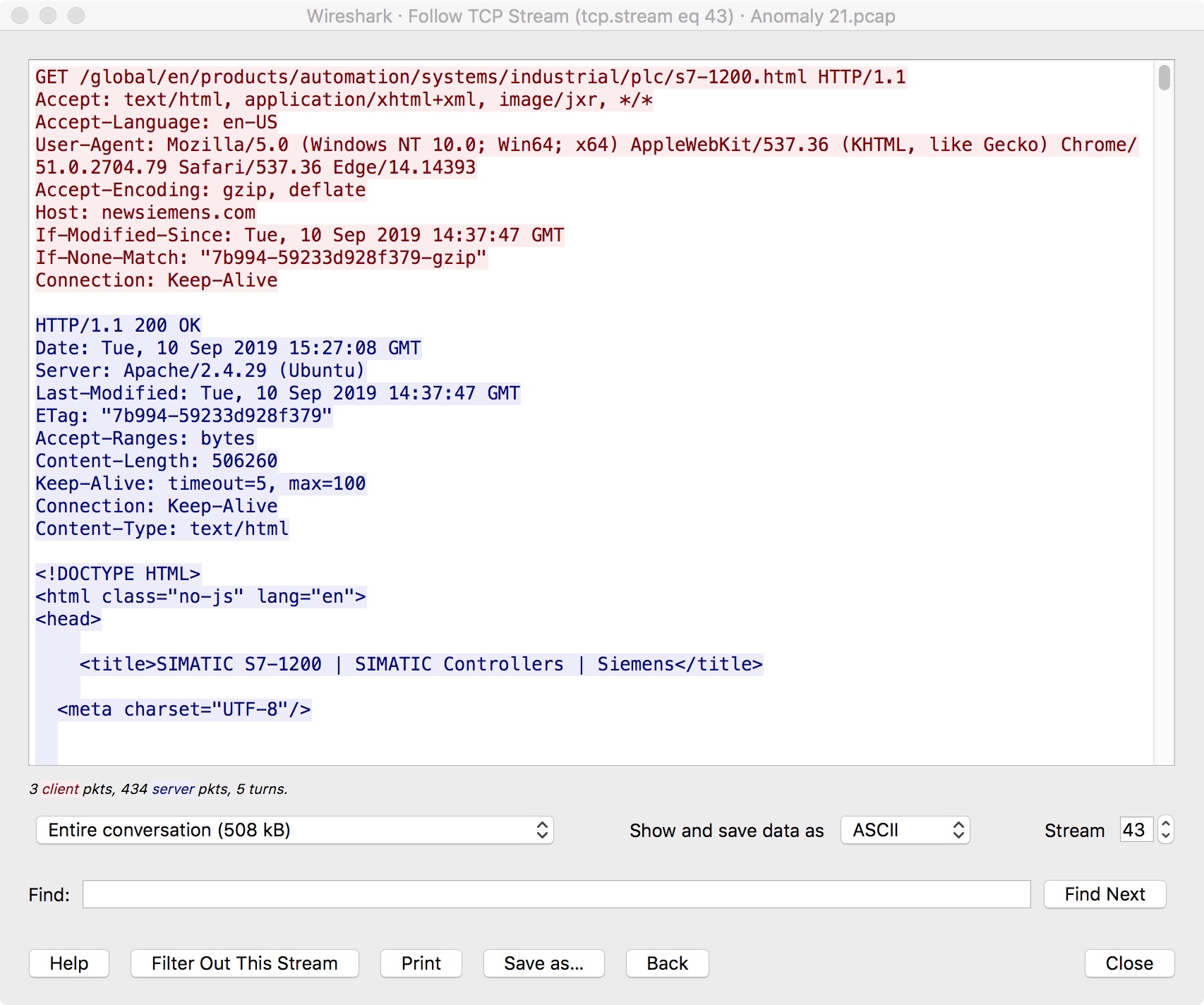
We can see that the attacker’s server responded with an HTML document. Plain old HTML isn’t interesting, but embedded JavaScript usually contains juicy stuff. In fact, if we scroll down a bit, we can see this script that looks suspicious:
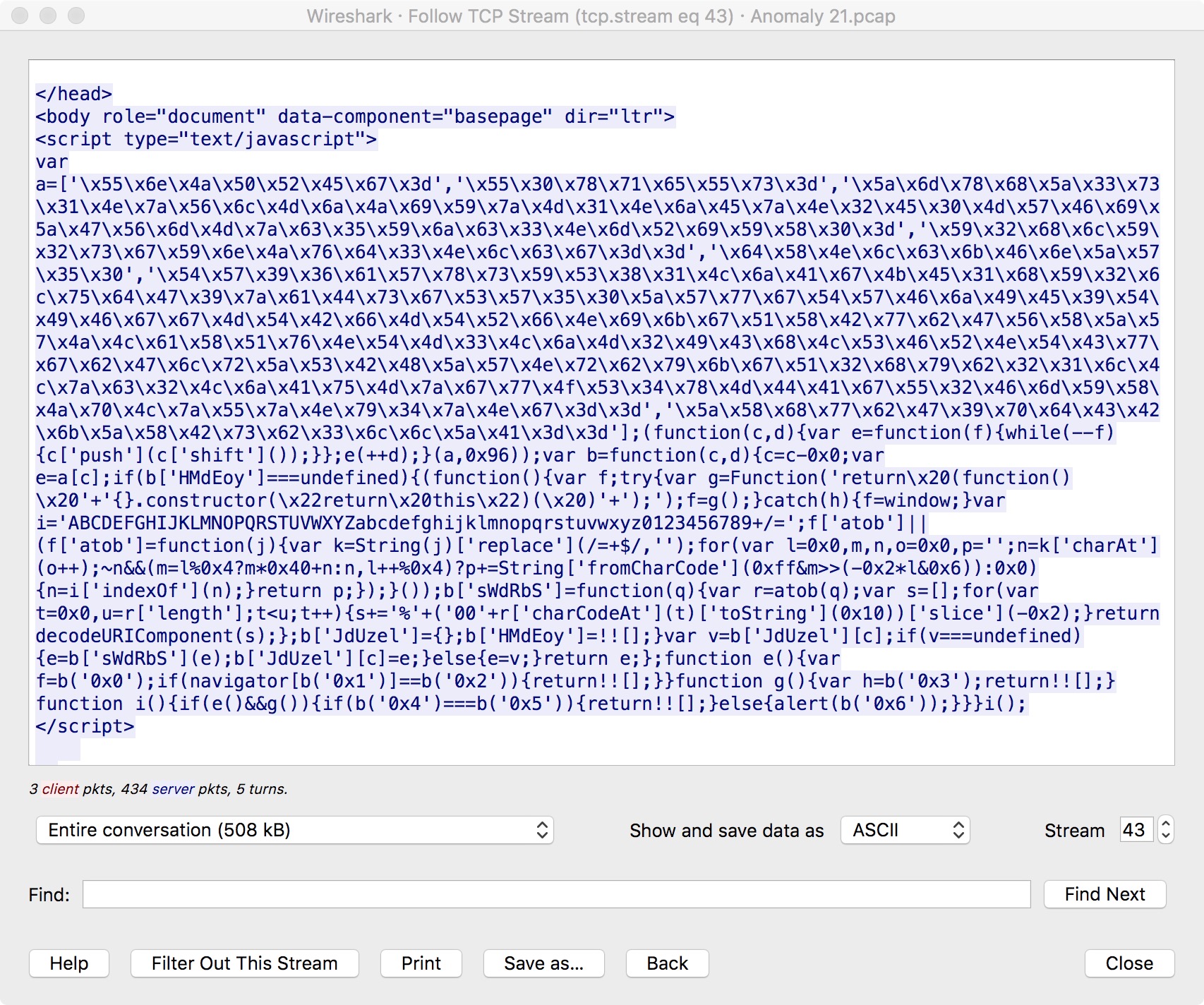
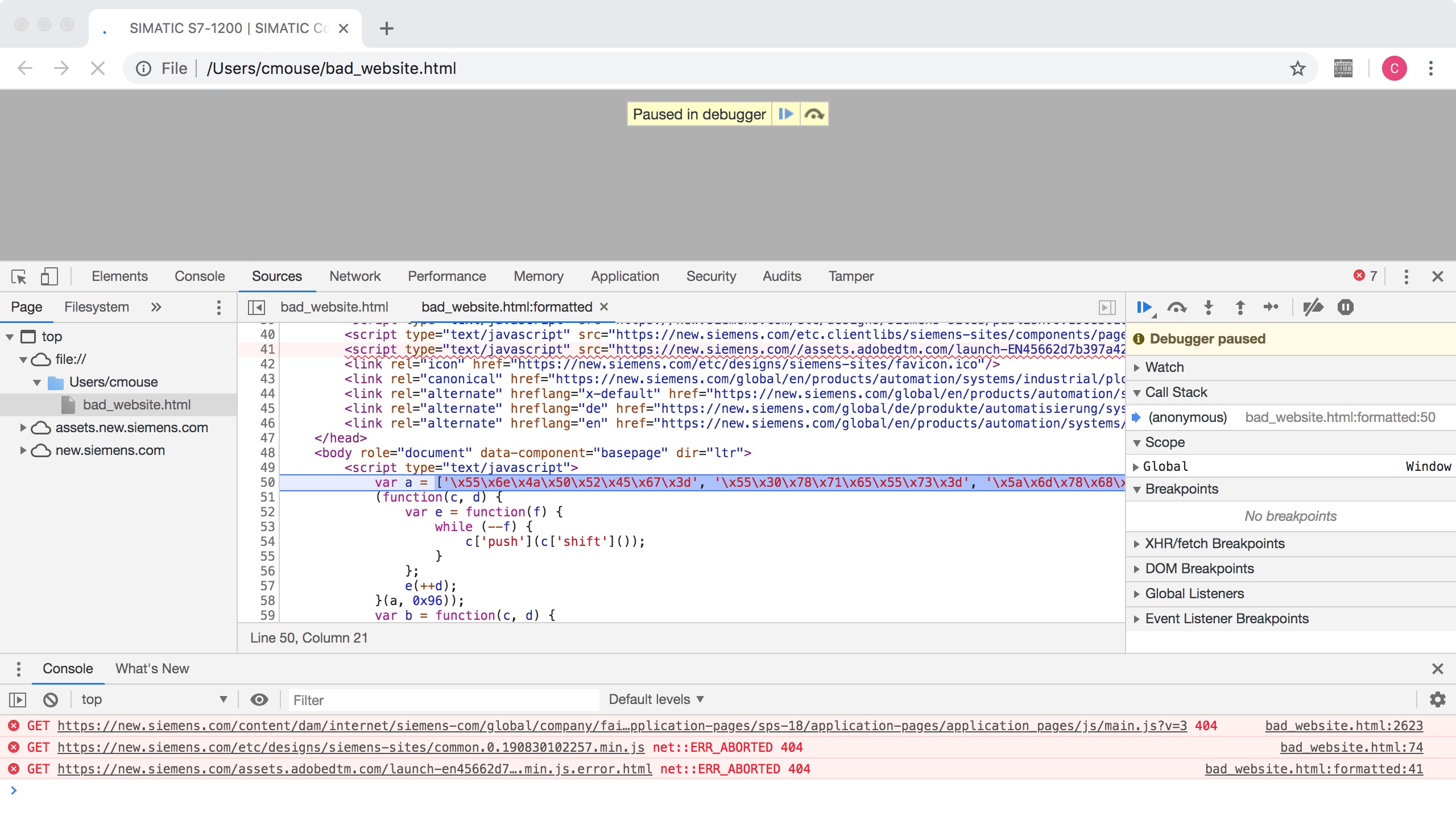
We can step through this code to figure out what it does. First, let’s copy the entire HTML document into a file, which we will call bad_website.html. Next, we can open the file in Google Chrome. Then, we can start debugging the code with Google Chrome’s Developer Tools.
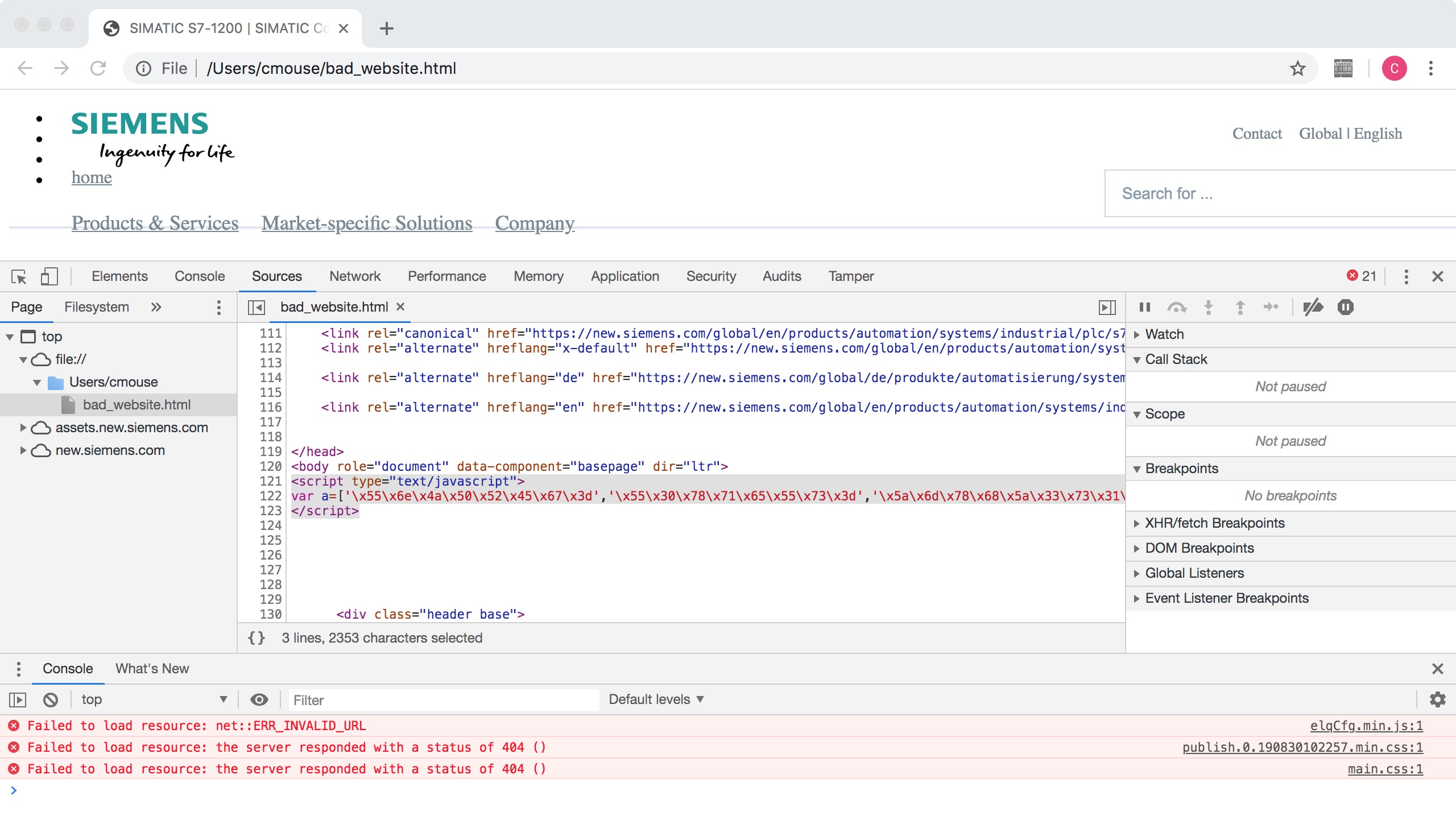
We are interested in the script on line 122. Click on the pause button at the top-left of the rightmost panel to pause script execution. Then reload the page to pause execution at the beginning of the script. We can click on the little brackets at the bottom-left of the code panel, which will prettify the code and make it MUCH easier to read. Your screen should look like this:
We can then step through the code with the buttons at the top of the rightmost panel like with any other debugger. We can see the values of variables in the “Scope” tab of the rightmost panel. After stepping over the first line, we can see that a is an array of 7 strings (note that the scope of a is global):
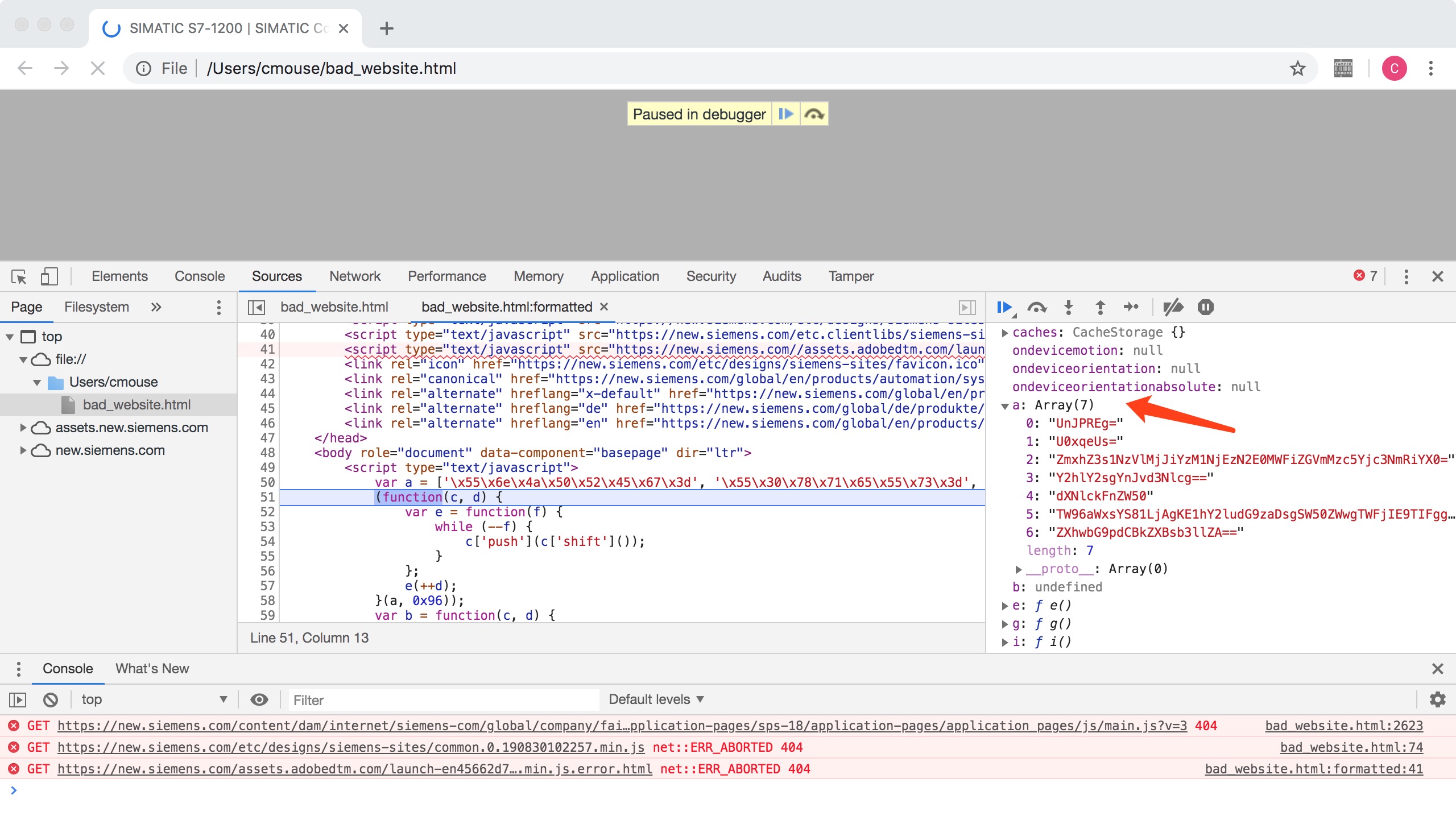
Apparently, these strings are Base64-encoded. The decoded strings are:
1 | RrODH |
575e22bc356137a41abdef379b776dba is the correct answer, but out of curiosity, we’ll step through the rest of the code to see what it’s doing.
The next 8 lines simply rearrange the order of the strings in array a:
1 | (function(c, d) { |
c['shift'] pops out and returns the element at the front of the array, and c['push'] pushes that element onto the end of the array. This process repeats for 0x96 times, so the resulting array is:
1 | check browser |
I won’t go into the details here, but function b(x) essentially returns the xth element of the rearranged array a. So function e returns true if the user agent is “Mozilla/5.0 (Macintosh; Intel Mac OS X 10_14_6) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/76.0.3809.100 Safari/537.36”:
1 | function e() { |
Function g sets variable h to “exploit deployed” and always returns true:
1 | function g() { |
Function i only alerts the flag if both e() and g() return true. Finally, function i is called:
1 | function i() { |
Thus we know that the flag is “575e22bc356137a41abdef379b776dba”, but the compromise was likely not successful, since we can see from the packet capture that the user agent is “Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.79 Safari/537.36 Edge/14.14393”, which does not match the target user agent.
Trivia:
“Shimo La Kumwagilia” means “watering the hole” in Swahili.
![Simba (Source [2])](/images/cyberforce/anomaly-21-simba.png)
References:
[1] What is watering hole attack? - Definition from WhatIs.com, https://searchsecurity.techtarget.com/definition/watering-hole-attack
[2] By Source (WP:NFCC#4), Fair use, https://en.wikipedia.org/w/index.php?curid=62188679