Anomaly 45
Points: 78
This is a simple “login” program for the Nuclear Power Plant. This program was created with no intention of security, so it was designed to have a single user and a single password. What is the flag? Answer format: flag {hidden_flag}
The provided file is a 32-bit ELF executable. First, we can run strings on the executable. Among the results are:
1 | Username: |
We can guess that the username is “peuFTW”.
Then, we can disassemble the executable with IDA Pro (or, alternatively, with objdump, as this executable isn’t very complicated). We can see that the majority of the functionality is in the method peu. Let’s take a look at this method:
1 | .text:000005D4 call __x86_get_pc_thunk_bx |
peu calls __x86_get_pc_thunk_bx, which “loads the position of the code into the %ebx register, which allows global objects (which have a fixed offset from the code) to be accessed as an offset from that register”. [1] Thus %ebx will hold the value of 0x2000 (0x5D9 + 0x1A27) and serve as the base address for referencing global strings.
1 | .text:000005F8 lea eax, [ebp+var_19] |
peu reads user input and stores it at ebp+var_19.
1 | .text:0000060E lea eax, [ebx-1872h] |
It then compares the user input with a global string at ebx-1872h, which we know is 0x78E. The string stored at 0x78E is “peuFTW”. Thus we know this is the correct username.
1 | .text:0000065C lea eax, [ebp+var_20] |
peu reads user input again and stores it at ebp+var_20.
1 | .text:0000066F mov eax, [ebp+var_20] |
It then compares the user input with 0x712. Thus we know the correct password is 0x712, which is 1810 in decimal.
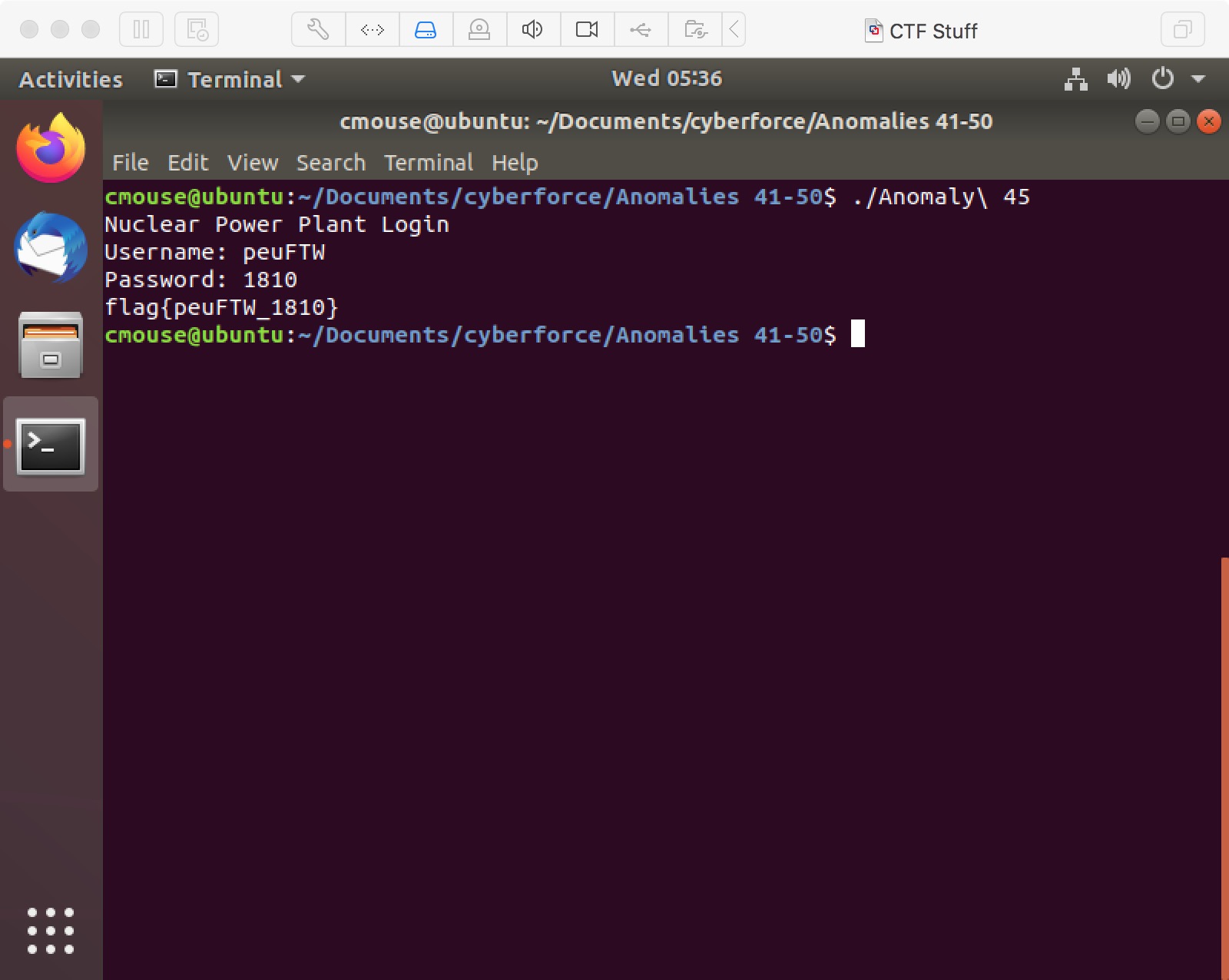
Running the executable, we see that this is indeed the correct credentials:
References:
[1] https://stackoverflow.com/questions/6679846/what-is-i686-get-pc-thunk-bx-why-do-we-need-this-call